AI-Powered Attacks Target FortiGate Devices Using CyberStrikeAI
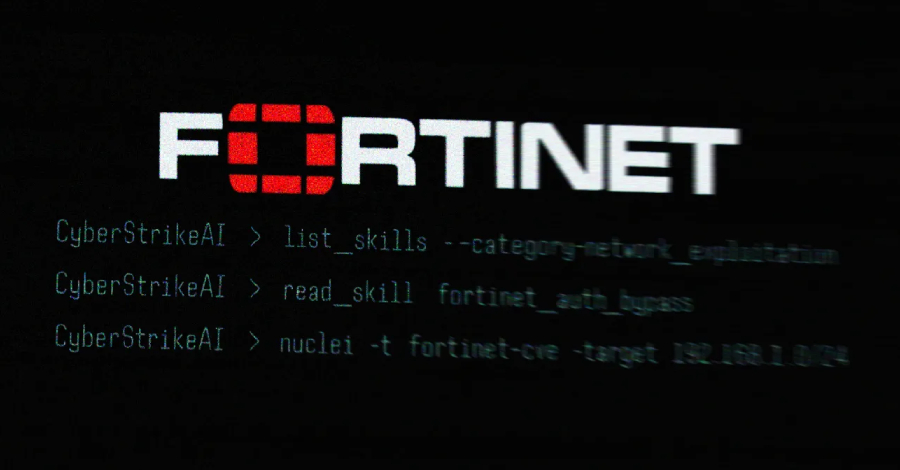
New evidence has surfaced revealing that threat actors utilized an open-source, AI-native security testing platform called CyberStrikeAI to launch a wave of cyberattacks against Fortinet FortiGate appliances across 55 countries. The findings, uncovered by security experts at Team Cymru, shed light on the increasing role of artificial intelligence in sophisticated, large-scale cyber operations.
Tracing the Source: Key Findings from Team Cymru
The investigation began when Team Cymru analyzed the IP address 212.11.64[.]250, linked to a suspected Russian-speaking threat actor. This entity conducted automated mass scanning, searching for vulnerable FortiGate appliances worldwide. Through this analysis, researchers discovered the use of CyberStrikeAI, an advanced offensive security tool that leverages AI to identify weaknesses in target systems.
What is CyberStrikeAI?
CyberStrikeAI is an open-source offensive security toolkit developed by a China-based programmer known online as Ed1s0nZ. According to its GitHub repository, the platform is written in Go and integrates over 100 security tools. Its capabilities span vulnerability discovery, attack-chain analysis, knowledge retrieval, and visualization of results, making it a powerful resource for both penetration testers and malicious actors.
Security researcher Will Thomas (also known as @BushidoToken) noted that Ed1s0nZ appears to have connections to Chinese government-linked organizations. CyberStrikeAI’s versatility and AI-driven modules make it particularly effective for automating complex attack chains and rapidly identifying vulnerable infrastructure.
Scope and Scale: Global Impact of the Attacks
The scale of the CyberStrikeAI-powered campaign is striking. According to a report by Amazon Threat Intelligence, the attacker systematically targeted FortiGate devices using generative AI services such as Anthropic Claude and DeepSeek. These efforts resulted in the compromise of more than 600 appliances across 55 countries, highlighting the global reach and efficacy of AI-assisted offensive operations.
Between January 20 and February 26, 2026, Team Cymru identified 21 unique IP addresses running CyberStrikeAI, with the majority of servers hosted in China, Singapore, and Hong Kong. Additional infrastructure was detected in the United States, Japan, and Switzerland, underscoring the tool’s international deployment.
The Developer Behind CyberStrikeAI and Related Tools
The prolific developer Ed1s0nZ maintains several other tools aligned with offensive security and AI exploitation. These include:
- Watermark-tool: Adds invisible digital watermarks to documents.
- Banana_blackmail: A Golang-based ransomware tool.
- PrivHunterAI: Uses AI models like Kimi, DeepSeek, and GPT to detect privilege escalation vulnerabilities.
- ChatGPTJailbreak: Contains prompts for bypassing ChatGPT’s restrictions.
- InfiltrateX: Scans for privilege escalation vulnerabilities.
- VigilantEye: Monitors databases for leaks of sensitive information and sends alerts via WeChat Work bots.
These projects reflect Ed1s0nZ’s ongoing interest in both AI security research and the development of tools that can be used for both legitimate and malicious purposes.
Connections to Chinese State-Sponsored Cyber Operations
Security researchers have observed that Ed1s0nZ interacts with organizations linked to Chinese government cyber operations. Notably, the developer has engaged with Knownsec 404, a prominent Chinese security vendor that suffered a major data breach in late 2025. This leak revealed extensive ties between the company and Chinese state security agencies, including the Ministry of State Security (MSS) and the People’s Liberation Army (PLA).
Analysis by DomainTools characterized Knownsec 404 not just as a cybersecurity vendor, but as a “state-aligned cyber contractor” with capabilities that support Chinese intelligence and military objectives. Tools such as ZoomEye and the Critical Infrastructure Target Library have enabled China to map millions of foreign IPs, domains, and organizations based on sector and strategic value.
Efforts to Obscure State Ties
Recent GitHub activity shows Ed1s0nZ removing references to having received a Level 2 Contribution Award from the China National Vulnerability Database (CNNVD). This move is seen as an attempt to obscure potential state connections as CyberStrikeAI gains prominence and scrutiny in the global cybersecurity community.
China operates two primary vulnerability databases: CNNVD, managed by the MSS, and CNVD, overseen by CNCERT. Studies have shown that CNNVD sometimes delays publishing critical vulnerabilities, raising concerns about the possible use of undisclosed flaws in state-sponsored campaigns. Attempts by CyberStrikeAI’s developer to distance themselves from CNNVD suggest a strategic effort to maintain the tool’s operational viability as its adoption spreads worldwide.
The Proliferation of AI-Augmented Offensive Security Tools
Experts warn that the adoption of CyberStrikeAI represents a significant shift in the offensive cybersecurity landscape. As AI-driven tools become more accessible and sophisticated, the potential for large-scale, automated attacks increases. The CyberStrikeAI campaign against FortiGate devices may serve as a blueprint for future threats, prompting defenders to enhance their detection and mitigation strategies for AI-powered attacks.
This article is inspired by content from Original Source. It has been rephrased for originality. Images are credited to the original source.